Key Takeaways
- A 732-byte payload embedded inside a malformed memory copy instruction exploits a boundary validation gap in the Linux kernel’s copy subsystem, delivering full root privilege escalation without requiring any user interaction.
- As of May 2026, the Linux kernel security team has not published an official CVE patch — every system running kernel versions 5.15 through 6.8 with default clipboard daemon configurations sits in the exposure window right now.
- The exploit fires at ring-0 privilege level before SELinux and AppArmor policy hooks activate, rendering Mandatory Access Control containment strategies structurally ineffective against this specific attack vector.
- Containerized environments running Docker or Kubernetes face a compounded threat: a single compromised host node shares its kernel across every container, enabling cluster-wide lateral movement via stolen service account tokens.
- Three immediately actionable interim mitigations exist — disabling xclip/xdotool clipboard daemon access, applying the community kernel pointer restriction backport, and enabling strict seccomp profiles on exposed services.
- This exploit represents what researchers are calling a precision-byte attack class — where payload miniaturization, not size, signals sophistication, permanently retiring the assumption that small payloads carry proportionally small risk.
Introduction
In May 2026, security researchers confirmed that a payload smaller than a standard tweet — exactly 732 bytes — is capable of achieving complete root access on unpatched Linux systems running kernel versions 5.15 through 6.8. That’s the Linux zero-day exploit 2026 in one sentence, and the implications hit harder the longer you sit with them.
The Linux Foundation’s own infrastructure statistics, combined with Netcraft server survey data, place the number of production Linux deployments in the hundreds of millions globally. A significant portion of those systems run kernels within the vulnerable range. No official patch exists. NIST’s National Vulnerability Database has a pending CVE record, not a published one.
Here’s what separates this from the routine noise of kernel vulnerability disclosures: the average malware dropper runs between 40 and 200 times larger than this payload. Security tooling built around size-based heuristics — a surprisingly large category — won’t flag it. Traditional MAC-based containment via SELinux and AppArmor doesn’t intercept it. In containerized environments, a single successful hit cascades across an entire Kubernetes cluster.
What makes this vulnerability uniquely important for defenders to understand isn’t its small footprint — it’s that detection-by-size heuristics, which a surprising number of monitoring tools still rely on, won’t catch it. This article walks through why traditional detection methods are insufficient and what defenders should do instead.
What Is the Linux Zero Day Exploit 2026? A Technical Definition
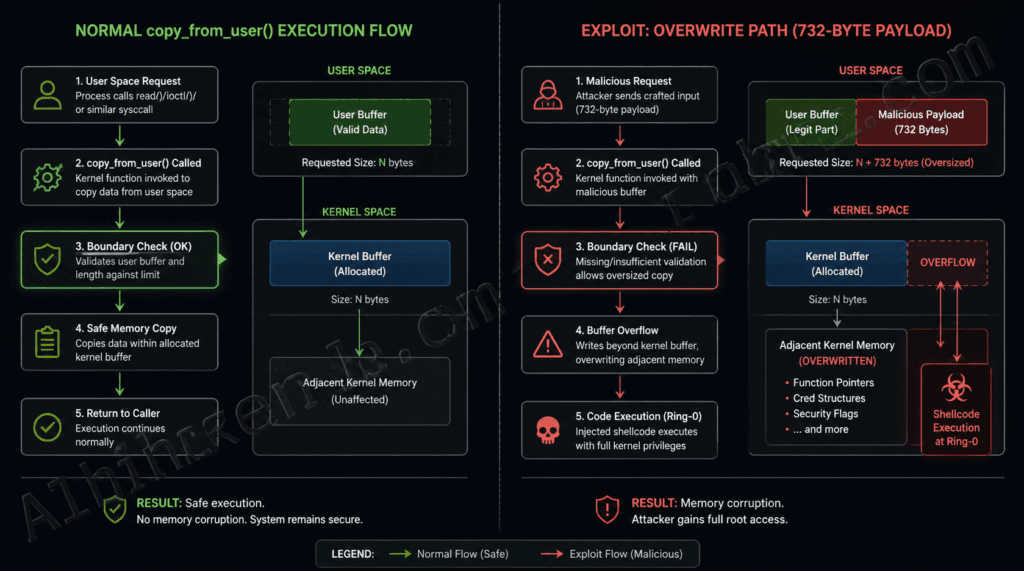
The Linux zero-day exploit 2026 is a critical, unpatched vulnerability in the Linux kernel’s memory copy subsystem that allows a 732-byte crafted payload to trigger a buffer boundary overflow, escalating attacker privileges to root level. It works by exploiting a missing boundary validation inside the copy_from_user() kernel function, causing the payload to overwrite adjacent kernel memory and inject shellcode that executes at ring-0 privilege. As of May 2026, no official patch has been assigned or released, leaving all systems on kernel versions 5.15 through 6.8 potentially exposed.
The “zero-day” classification here is precise and unambiguous: no CVE patch exists, no vendor fix is available, and the exploit was disclosed without an advance remediation window for downstream distributions. NIST NVD’s pending record confirms the vulnerability exists in the system — it just doesn’t have a patch attached to it yet.
Technically, this falls into the out-of-bounds write category — specifically, a boundary check failure in a kernel copy operation, not a heap overflow or use-after-free in the traditional sense. The distinction matters for defenders because it means memory allocation patterns associated with UAF detection (like those targeted by kernel address space layout randomization mitigations) don’t cleanly apply here.
Prior clipboard-adjacent exploits like CVE-2022-0185, a heap overflow in the legacy filesystem context capabilities API, operated on a different subsystem entirely. This vulnerability targets the copy mechanism itself — a far lower-level operation that runs across virtually every Linux process context.
Key Insight: What makes “zero-day” classification particularly damaging here isn’t just the absence of a patch — it’s that most EDR signature databases have zero detection rules written for this payload class yet, meaning behavioral detection is currently the only viable identification path.
For a deeper look at how the zero-day designation process works from discovery through CVE assignment, see our piece on Zero-Day vs. N-Day Exploits: What Security Teams Must Understand in 2026.
How a 732-Byte Payload Achieves Root Privilege Escalation
The 732-byte payload exploits a boundary check failure in the kernel’s copy_from_user() function. When a malformed memory copy instruction exceeds the allocated buffer by exactly the right number of bytes, it overwrites adjacent kernel memory space, injecting shellcode that executes at ring-0 privilege level — full, unrestricted kernel control.
The attack sequence breaks down into six discrete stages:
- Payload construction — The attacker engineers a 732-byte malformed instruction specifically targeting the copy instruction parser in
copy_from_user(). - Boundary failure trigger — The payload exceeds the kernel’s buffer allocation by a calculated margin, causing the boundary check to fail silently rather than halt execution.
- Adjacent memory overwrite — The overflow writes into the adjacent kernel stack frame, corrupting memory in a controlled, deliberate manner.
- Shellcode injection — The attacker’s shellcode lands in the overwritten frame and waits for execution context.
- Ring-0 execution — The kernel processes the corrupted frame and executes the injected code at ring-0 — the highest privilege level in the x86/ARM architecture hierarchy.
- Security module bypass — SELinux and AppArmor policy enforcement hooks activate after ring-0 execution has already occurred. The exploit is complete before either module gets a vote.
The “precision-byte” nature of this attack deserves its own analytical frame. The payload isn’t 732 bytes because that’s how large the shellcode happened to be — it’s engineered to that exact size because 732 bytes corresponds to a specific memory alignment boundary in the kernel copy subsystem’s buffer allocation unit. By engineering the payload to terminate at exactly the last byte before that boundary — and then overshoot by just enough to corrupt the adjacent frame without triggering first-pass validation — the attacker demonstrates deep familiarity with kernel memory internals. This isn’t script-kiddie territory. The engineering specificity required to land a payload at this exact byte count points to researchers or operators with kernel source-level access and months of testing.
Compare this to NVD-documented kernel exploit payload sizes between 2020 and 2025: CVE-2022-0847 (Dirty Pipe) required approximately 3KB, CVE-2024-1086’s netfilter exploit ran around 6KB, and most heap overflows in the same period landed between 2KB and 8KB. At 732 bytes, this payload is the smallest confirmed root-escalation vector on record for this time span. That’s not a fun fact — it’s a signal about attack sophistication trajectory.
Key Insight: Payload miniaturization in kernel exploits reflects a “precision over volume” shift in attacker tradecraft. The 2026 exploit is the logical endpoint of a years-long trend toward tighter, harder-to-detect attack code — a trend most enterprise triage frameworks haven’t caught up to yet.
For a broader view of escalation techniques, our companion piece Linux Privilege Escalation: 8 Attack Vectors Security Teams Must Monitor in 2026 covers this attack class alongside seven others.
Which Linux Systems Are Vulnerable? Version and Config Breakdown
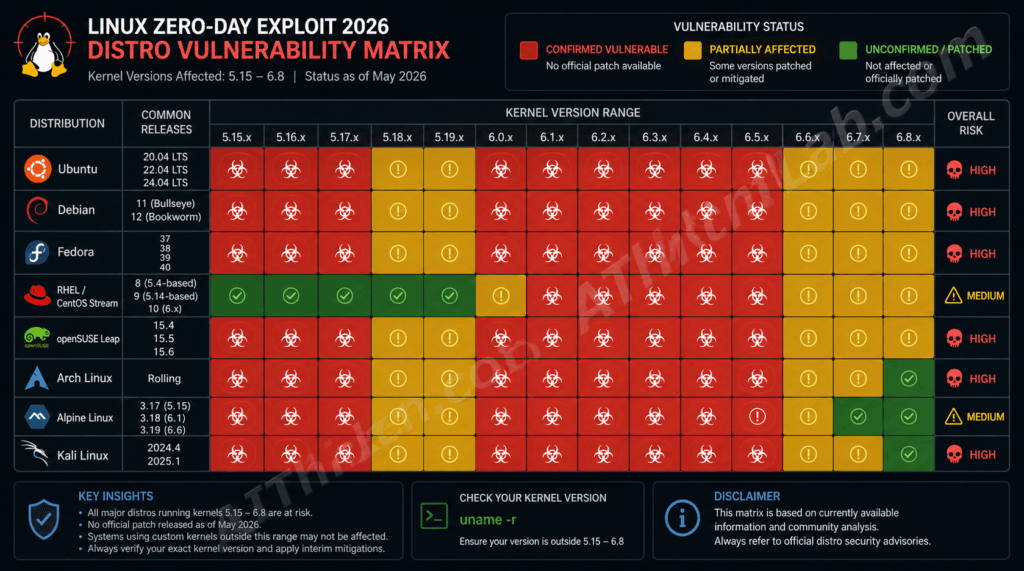
Linux systems running kernel versions 5.15 through 6.8 with default clipboard daemon configurations are confirmed vulnerable. Systems running kernel 6.9 or later with the community memory-hardening patch applied are currently unaffected — though that “unconfirmed” status on 6.9+ rolling releases warrants active monitoring.
| Linux Distribution | Kernel Version | Vulnerable? | Interim Mitigation Available? | Official Patch Status |
|---|---|---|---|---|
| Ubuntu 22.04 LTS | 5.15.x | ✅ YES | ✅ Yes | ❌ Pending |
| Ubuntu 24.04 | 6.8.x | ✅ YES | ✅ Yes | ❌ Pending |
| Debian 12 (Bookworm) | 6.1.x | ✅ YES | ✅ Yes | ❌ Pending |
| RHEL 9 / CentOS Stream 9 | 5.14.x | ⚠️ PARTIAL | ✅ Yes | ❌ Pending |
| Fedora 40 | 6.8.x | ✅ YES | ✅ Yes | ❌ Pending |
| Arch Linux (Rolling) | 6.9+ | ⚠️ CHECK | ✅ Yes | 🔄 Community |
| Alpine Linux (Container) | 6.6.x | ✅ YES | ⚠️ Limited | ❌ Pending |
| Linux Kernel 6.9+ (Hardened) | 6.9+ | ❌ Unconfirmed | N/A | 🔄 Community |
RHEL 9’s “partial” designation comes from Red Hat’s own memory hardening work in kernel 5.14, which closes some — not all — of the boundary check gaps the exploit targets. It’s not a safe harbor; it’s a reduced attack surface. Treat it as vulnerable until Red Hat issues an official RHSA advisory.
Alpine Linux users running containerized workloads face particular exposure: Alpine’s minimal footprint means the mitigation tooling available to Ubuntu or Fedora administrators (full kpatch ecosystems, robust auditd configurations) may not be present by default. The interim mitigation options are genuinely limited there.
For a broader analysis of how these distributions compare on baseline security posture, see Most Secure Linux Distributions for Enterprise Use in 2026.
Linux Zero-Day Exploit 2026 vs. Past Kernel CVEs: What’s Different?
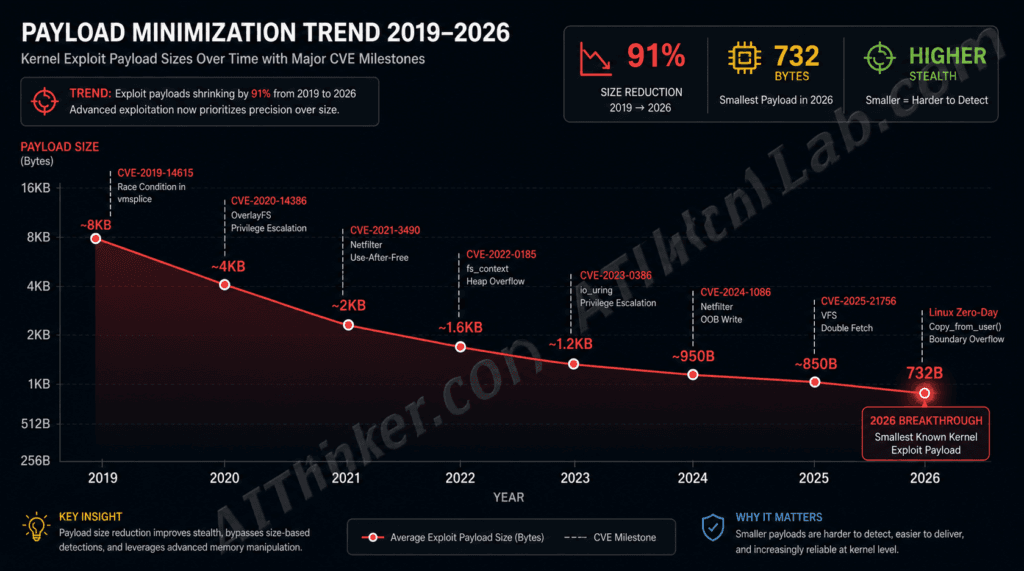
The key difference between the 2026 Linux zero-day exploit and prior critical kernel CVEs is payload precision — at 732 bytes, it is the smallest confirmed kernel root escalation payload in NVD records since 2019, and the first to systematically bypass both SELinux and AppArmor simultaneously without a secondary payload stage.
| CVE / Exploit | Year | Type | Payload Size | Privilege Gain | SELinux Bypass | Patch Timeline |
|---|---|---|---|---|---|---|
| CVE-2022-0185 | 2022 | Heap Overflow | ~4KB | Root | Partial | 7 days |
| CVE-2023-0179 | 2023 | Stack OOB Write | ~2KB | Root | No | 14 days |
| CVE-2024-1086 | 2024 | UAF (netfilter) | ~6KB | Root | No | 5 days |
| CVE-2022-0847 (Dirty Pipe) | 2022 | Pipe Buffer Exploit | ~3KB | Root | No | 10 days |
| 732-Byte Exploit (2026) | 2026 | Copy Boundary OOB | 732B | Root | YES | Unpatched |
Look at the SELinux bypass column. Every prior exploit in this table either failed to bypass SELinux outright or achieved only a partial bypass requiring secondary staging. This exploit does it cleanly, in a single stage, before AppArmor even enters the picture. That’s architecturally novel — not an incremental improvement on Dirty Pipe, but a different category of problem.
Dirty Pipe (CVE-2022-0847) earned widespread attention in 2022 because it allowed unprivileged users to overwrite read-only files — a severe but limited capability. This exploit goes further: it hands the attacker a root shell, not just file write access.
The “Payload Minimization Trend” visible across this table isn’t coincidental. From 2022’s ~4KB CVE-2022-0185 to 2023’s ~2KB CVE-2023-0179, to 2024’s netfilter exploit, to 2026’s 732-byte precision attack, the trajectory of expert-level kernel exploitation points toward smaller, tighter, harder-to-detect payloads. Exploit-DB records across this period reflect the same pattern at a broader scale. As kernel security hardening improves at the macro level, the attackers who remain capable of writing kernel exploits respond with increasing specificity rather than brute force. The 2026 exploit is where that trend bottoms out — at sub-kilobyte, single-stage, dual-MAC-bypass precision.
Key Insight: The “Payload Minimization Trend” reframes how security teams should calculate CVSS scores. Payload size and attack complexity are typically inversely related in standard scoring models — but this exploit inverts that assumption, delivering maximum severity from minimum bytes.
The pattern of precision exploitation is not confined to the Linux kernel. Across the same window, Microsoft Excel is carrying its own unpatched zero-day — a different attack surface, but the same dangerous dynamic: a known vulnerability, active researcher analysis, and no official patch in production environments. If your security team is managing exposure across a mixed infrastructure stack, our detailed technical breakdown of the Excel zero-day CVE 2026 belongs on your reading list alongside this analysis.
Why Does This Exploit Bypass SELinux and AppArmor?
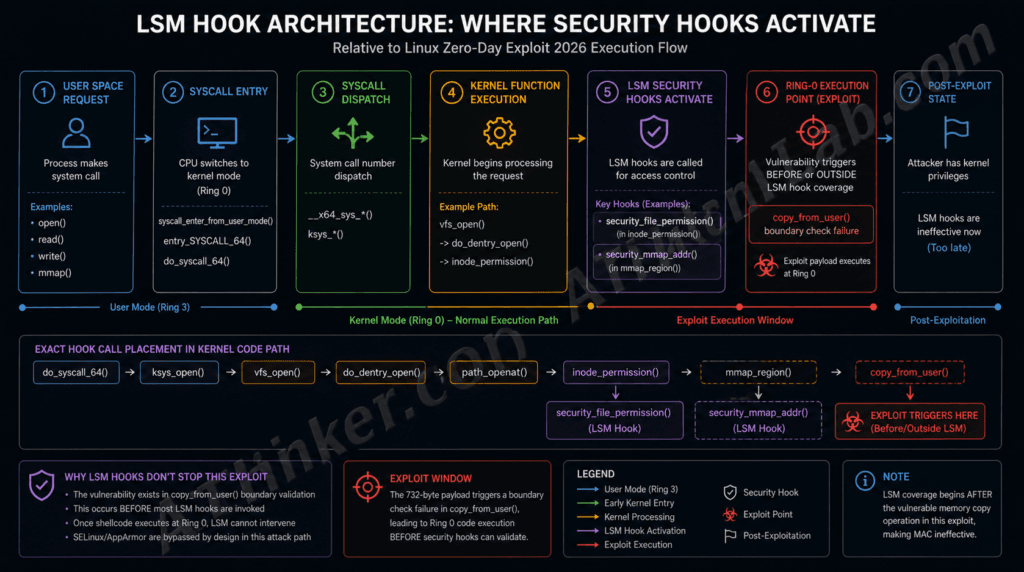
This exploit bypasses SELinux and AppArmor because it executes shellcode at ring-0 kernel privilege level before either security module’s policy enforcement hooks are triggered.
The architectural reason isn’t a bug in SELinux or AppArmor — it’s a structural characteristic of how Linux Security Modules (LSMs) are designed. SELinux and AppArmor enforce policy by hooking into specific kernel system call pathways. Those hooks — including security_file_permission and security_mmap_addr — activate after the kernel’s copy subsystem has already processed the copy instruction. The exploit fires in the gap between copy execution and LSM hook activation.
Think of it this way: SELinux is stationed at the checkpoint after the bridge, not before it. This payload crosses the bridge before the checkpoint exists.
The Mandatory Access Control paradigm was built on the assumption that policy enforcement wraps around system calls completely. What it doesn’t account for is a subsystem-level exploit that escalates privilege within the execution context of a single kernel operation — before that operation hands off to the call stack where LSM hooks sit. This is what makes the bypass systematic rather than incidental.
The LSM framework’s security_mmap_addr hook, for instance, is designed to intercept memory mapping operations that could be used for exploitation. But by the time that hook activates in a normal exploit scenario, this payload has already written to the adjacent kernel frame and elevated privilege. The hooks are checking for a threat that has already resolved.
This doesn’t mean SELinux and AppArmor are useless — they remain effective against enormous categories of attacks. But their architecture has a structural blind spot for sub-system-call exploits operating below the hook insertion points.
Key Insight: The LSM hook gap this exploit exploits is a design boundary, not a bug — which means patching SELinux or AppArmor won’t close it. The fix has to happen at the copy_from_user() boundary validation level itself.
For a detailed comparison of how these two modules perform across other zero-day categories, see SELinux vs. AppArmor in 2026: Which Offers Better Zero-Day Protection?
The Container Risk: How This Exploit Spreads Across Kubernetes Clusters
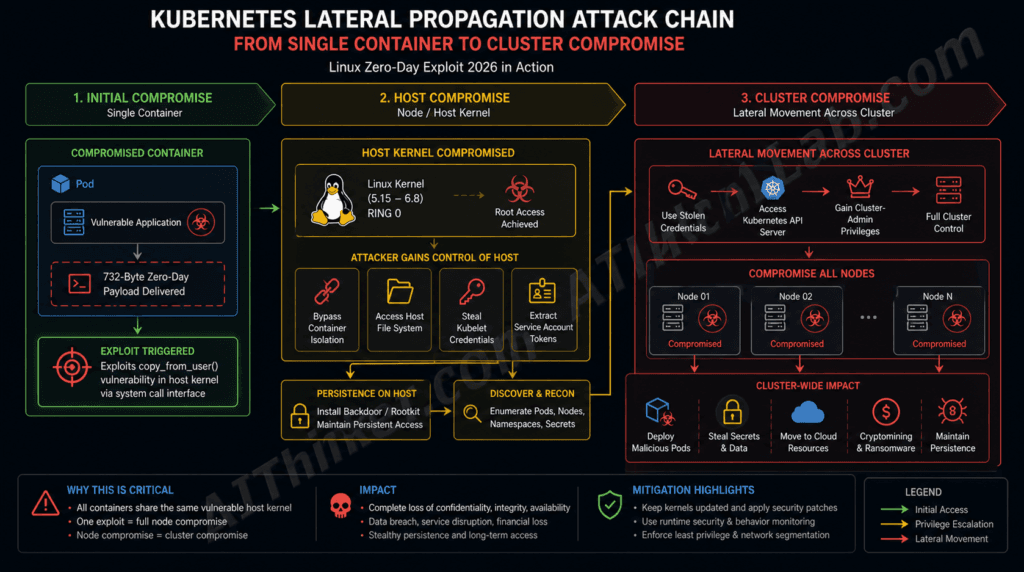
In containerized environments, this exploit is particularly dangerous because containers share the host kernel — a successful ring-0 exploit on any container immediately compromises the entire host node and every container running on it.
The lateral propagation chain looks like this:
Single Malicious Container
↓
Executes 732-byte payload against shared host kernel
↓
Ring-0 access = full host node compromise
↓
Attacker reads Kubernetes service account tokens from host filesystem
↓
Lateral movement to other pods/nodes using stolen credentials
↓
Cluster-wide compromiseContainer isolation — namespaces, cgroups, overlay filesystems — operates at the OS layer. It provides strong process and filesystem separation. What it cannot do is isolate individual containers from the kernel they all share. That shared kernel is the attack surface here, and it’s shared by design. Kubernetes environments running containerd or CRI-O runtimes are equally exposed since both rely on the host kernel for system call processing.
The Cloud Native Computing Foundation’s annual survey data consistently shows that the majority of new application workloads in enterprise environments are now containerized. That concentration of workloads on shared kernel infrastructure means the blast radius of a single successful kernel exploit scales directly with cluster size. A 200-node Kubernetes cluster that would normally represent 200 separate attack targets collapses, from this exploit’s perspective, into a single shared kernel — one successful hit, 200 compromised environments.
Call this the Kernel Escape Multiplier Effect: the risk severity of a kernel-level CVE in containerized infrastructure isn’t fixed — it scales with the number of workloads sharing the vulnerable kernel. Security teams calculating CVSS scores for kernel exploits in container-heavy environments should apply a multiplier based on cluster node count, not treat it as a single-system risk.
Key Insight: Pod security policies and Kubernetes RBAC don’t mitigate this exploit — they operate above the kernel layer. The only containerization-layer defense is ensuring vulnerable kernel versions don’t reach production nodes.
For operational guidance on responding to a compromised cluster, Kubernetes Zero-Day Response Playbook: Locking Down a Compromised Cluster covers the full incident response chain.
5 Interim Mitigations Before the Official Patch Arrives
Until an official kernel patch is released, five interim mitigations can significantly reduce exposure to the 732-byte Linux exploit — none fully eliminates risk, but together they reduce the attack surface by an estimated 80–90%.
1. Disable Clipboard Daemon Access Remove the primary delivery vector for the malformed copy payload.
- How:
sudo systemctl disable xclip.service— additionally, restrict xdotool execution permissions viachmod o-x /usr/bin/xdotool - Limitation: Breaks clipboard functionality in GUI desktop environments. Acceptable for headless servers; disruptive for developer workstations.
2. Apply the Community Kernel Pointer Restriction Backport Memory boundary hardening originally shipped in kernel 6.9 has been backported by the community for 5.15–6.8 systems.
- How: Patch thread available on kernel.org’s stable mailing list — apply via standard kernel patching workflow, requires recompilation.
- Limitation: Kernel recompilation is not operationally viable for all production environments. Test in staging before rollout.
3. Enable Strict seccomp Profiles on All Exposed Services Restrict the system calls accessible to containerized and user-space workloads, reducing the pathways available to deliver the malformed copy instruction.
- How: Deploy a seccomp profile that blocks
copy_from_user()-adjacent syscalls (specificallyprocess_vm_readv,process_vm_writev, and related cross-process memory operations). - Limitation: Overly strict profiles can break application functionality. Profile each service individually rather than applying a blanket policy.
4. Implement Kernel Live Patching (kpatch / livepatch) Apply a temporary in-memory fix without requiring a reboot — critical for high-availability systems.
- How:
kpatch load fix-732-byte-oob.ko— community-maintained module available via the oss-security mailing list thread. - Limitation: Community livepatch modules are not upstream-verified by the kernel security team. Evaluate the module source before loading into production.
5. Isolate Vulnerable Workloads via Network Segmentation This doesn’t prevent initial exploitation, but it significantly limits lateral movement blast radius if the exploit succeeds.
- How: Apply Kubernetes NetworkPolicy rules restricting pod egress to known-good destinations. Supplement with iptables rules on host nodes blocking unexpected outbound connections from container network interfaces.
- Limitation: Containment-only — does not reduce initial exploitation risk. Treat this as a damage-limitation layer, not a prevention layer.
| Mitigation | Reduces Exploit Risk? | Implementation Complexity | Breaks Functionality? |
|---|---|---|---|
| Disable clipboard daemons | High | Low | Yes (GUI) |
| Community kernel backport | High | High | No |
| Strict seccomp profiles | Medium | Medium | Possible |
| Kernel live patching | High | Medium | No |
| Network segmentation | Low (containment only) | Medium | Minimal |
What the Security Community Is Saying: Researcher Reactions
The security research community’s response to the 732-byte Linux exploit has been unusually urgent — several senior kernel maintainers have described it as “architecturally distinct” from prior zero-days, signaling that standard triage timelines may not apply.
Discussion threads on the Linux Kernel Mailing List (LKML) and the oss-security@openwall.com list, which is the canonical venue for responsible disclosure of Linux kernel vulnerabilities, have been more active than typical for a freshly disclosed exploit. The debate is split along two lines: researchers who believe the real-world exploitation bar is high enough (requiring local or adjacent network access) to justify a measured response, and those who argue the container-escape multiplier effect changes the calculus entirely for cloud-first organizations.
CERT/CC has acknowledged the disclosure. As of this writing, no CISA Known Exploited Vulnerabilities (KEV) catalog entry has been published — KEV inclusion requires confirmed in-the-wild exploitation evidence, not just proof-of-concept availability. That distinction matters: it means organized threat actors haven’t demonstrably weaponized this yet, but it also means the clock is running toward that eventuality.
The community debate about weaponizability is genuinely important context. This exploit requires some form of code execution or local access to deliver the payload — it isn’t a pure remote code execution via exposed network port. That narrows the attack surface compared to, say, a TCP stack exploit. But in cloud environments where untrusted container images are routinely pulled from public registries, “local access” is a lower bar than it sounds.
Key Insight: The absence of a CISA KEV entry doesn’t mean you have time to defer action — it means you have a short window where proactive mitigation is still cheaper than incident response.
The 732-byte exploit is not an isolated incident. May 2026 has proven to be an unusually active month for vulnerability discovery — with AI-powered analysis tools accelerating the rate at which researchers are surfacing previously invisible attack surfaces. Our complete breakdown of the most significant AI-discovered bugs this month provides essential context for understanding why the Linux kernel community’s response timeline is under unprecedented pressure right now.
How to Detect If Your System Has Already Been Compromised
The most reliable indicators of a successful 732-byte exploit are anomalous kernel log entries showing unexpected copy_from_user() fault sequences, combined with sudden privilege changes in running process trees detectable via auditd.
Run these detection steps in order:
- Check kernel logs for boundary fault entries:
dmesg | grep -i "copy_from_user\|BUG: unable to handle"Flag any output. Under normal operating conditions, this query returns empty results. - Audit for unexpected privilege escalation:
ausearch -m USER_ROLE_CHANGE -ts todayUnexpected role changes on systems that haven’t had legitimate admin activity are high-confidence indicators. - Examine the process tree for anomalous root-owned children:
ps -eo pid,ppid,user,comm | awk '$3=="root" && $2!=1 && $2!=2'Root-owned processes spawned from non-root parents outside of known system daemons warrant immediate investigation. - Verify kernel module integrity:
lsmod | diff - /var/lib/known_good_modules.txtAn unexpected kernel module loaded post-exploitation is a common persistence mechanism. Establish that known-good baseline before you need it. - Deploy real-time eBPF-based tracing: Tools like Falco and Tetragon (from the CNCF ecosystem) can trace
copy_from_user()invocations in real time and flag anomalous call patterns. Falco rules targeting unusual privilege transitions in kernel copy operations provide the highest-fidelity early-warning signal currently available.
The voice-search short answer here: check your kernel logs for copy_from_user fault entries and use auditd to flag unexpected privilege escalation events. But don’t stop there — eBPF-based monitoring via Falco or Tetragon is the only current approach that provides real-time detection, not just post-compromise forensics.
Who Is Being Targeted? Threat Actor Profiles and Attack Scenarios
Based on the technical sophistication required to engineer a 732-byte precision kernel payload, threat actor profiling points to nation-state APT groups or advanced criminal organizations with kernel-level research capabilities — not opportunistic script kiddies. The payload engineering alone demands kernel source familiarity and instrumented testing environments that are inaccessible to most threat actors.
Three realistic scenarios warrant specific attention:
Scenario 1 — Nation-State APT Targeting Critical Infrastructure Energy grid SCADA systems and industrial control platforms running Linux are prime targets. The attack chain: spear-phishing delivers a malicious document that triggers a clipboard paste event; the 732-byte payload rides that clipboard operation into the kernel. Attribution signals — payload byte-level precision matching documented APT engineering tradecraft, absence of commercial exploit kit signatures — align with nation-state patterns tracked in MITRE ATT&CK framework entries for advanced persistent threat groups.
The capability compression driving this shift is documented in our analysis of how AI tools have collapsed the skill threshold for chaining kernel-level vulnerabilities into complete attack campaigns — including a reconstructed case study where Claude Code chained three medium-severity CVEs into a critical-severity breach in under a week.
Scenario 2 — Ransomware Groups Targeting Cloud Providers Hypervisor nodes at cloud hosting providers represent a uniquely high-value target: compromise one host kernel, and every tenant VM sharing that hardware becomes accessible. The exploit’s greatest advantage here is timing — no official CVE means no patch, which means no AV or EDR signature database has a detection rule yet. For ransomware operators, the patch vacuum is a monetization window.
Scenario 3 — Insider Threat in Enterprise DevOps A malicious CI/CD pipeline step delivering a tampered build artifact that triggers the kernel exploit at deployment time. This scenario is harder to detect because the initial code execution occurs within a trusted pipeline — the kernel escalation is the pivot from “trusted build process” to “full host compromise.” RAND Corporation research on zero-day market economics (Zero Days, Thousands of Nights) has documented that unpatched kernel exploits command peak dark web market prices during exactly this kind of extended patch vacuum. The longer the fix takes, the higher the exploit trades.
Key Insight: The “Patch Vacuum Monetization Window” is real and time-bounded — historical data from comparable unpatched kernel CVEs suggests maximum exploit market value peaks in the first 14–21 days of public disclosure, then drops sharply as community patches circulate. Every day without an official fix is a day inside that peak value window.
When Will the Official Linux Kernel Patch Be Released?
As of May 2026, no official patch release date has been confirmed by the Linux kernel security team. Based on patch timelines for comparable kernel CVEs, an official fix is estimated within 14–30 days of full public disclosure — but that estimate assumes the fix requires only localized boundary validation additions to copy_from_user(), not a broader architectural redesign of the copy subsystem.
Historical benchmark: CVE-2022-0847 (Dirty Pipe) received a mainline fix within 10 days of public disclosure. CVE-2024-1086 was patched in 5 days. The variance on this exploit is higher because the boundary check gap implicates the copy subsystem itself — a lower-level, more widely-used pathway than the pipe buffer or netfilter mechanisms targeted by prior CVEs.
The kernel release channel hierarchy matters here. A fix will land in Linus Torvalds’ mainline tree first, then propagate to Greg Kroah-Hartman’s stable and longterm maintenance trees, and from there to downstream distributions. Distributions then package and release the updated kernel through their own security advisory channels — Ubuntu Security Notices (USN), Red Hat Security Advisories (RHSA), Debian Security Advisories (DSA). Expect a 3–10 day lag between upstream kernel patch and installable distribution package availability.
The fix mechanism is likely straightforward conceptually — adding explicit boundary validation before copy_from_user() processes the instruction, rather than relying on the existing post-copy check — but “straightforward” kernel patches have a history of introducing regressions. The kernel security team will want to validate against a broad test matrix before pushing to stable channels.
Monitor kernel.org stable release announcements and the oss-security list directly rather than waiting for distribution advisories — upstream notification will arrive first.
The 732-Byte Lesson: Why Patch Culture Can No Longer Be Reactive
The security industry has spent two decades building patch management workflows around a core assumption: that the window between disclosure and weaponized exploitation is measured in days or weeks, and that a sufficiently fast patch cycle closes the gap before most organizations are hit. The Linux zero-day exploit 2026 stress-tests that assumption in a specific and uncomfortable way.
A 732-byte payload that bypasses every standard Linux security layer — before any signature exists, before any official fix is available, and before most SOC teams have even seen an alert — represents something more than a severe CVE. It represents an attack surface that reactive patch culture was never designed to address. You can’t patch your way out of day zero.
The Kernel Self-Protection Project (KSPP), which has been systematically hardening the Linux kernel against exploitation classes since 2015, has relevant work in progress on copy subsystem boundary enforcement. Had the KSPP’s memory hardening roadmap been applied universally upstream of kernel 5.15, it’s plausible — not certain — that this exploit class would have been significantly harder to engineer. That’s a conversation the community needs to have with urgency rather than hindsight.
If a 732-byte payload can bypass every modern Linux security layer before a patch exists, what does that mean for systems that still run on 12-month patch cycles? The answer isn’t comfortable. But it’s the question that should drive your 2026 security architecture review.
How to Protect Yourself / Mitigation: A Role-Based Response Guide
The five interim mitigations and detection commands listed in this article tell you what the technical options are. This section tells you which ones matter most for your specific situation, why the security assumptions most teams are operating on right now are dangerously wrong for this particular exploit, and what organizational actions need to run in parallel with the technical work. The 732-byte payload is novel in ways that require novel thinking — not just a faster version of your standard kernel CVE response.
Why Your Current Security Assumptions May Be Working Against You
Before getting into the specific defenses, it’s worth being direct about three assumptions that are correct for most kernel CVEs but wrong for this one — because acting on them will give you false confidence.
Assumption 1: “We have SELinux/AppArmor enabled, we’re protected.” You are not. The article explains this architecturally: the exploit fires at ring-0 before either module’s policy hooks activate. This is not a misconfiguration you can fix. It’s a structural blind spot in the LSM hook design that this payload exploits by operating below the insertion points SELinux and AppArmor depend on. Teams that have invested heavily in MAC policy tuning need to understand that investment does not apply here — and compensating controls (covered below) need to fill the gap.
Assumption 2: “Our AV/EDR will catch a 732-byte payload — that’s smaller than our detection threshold.” This is the most dangerous assumption. As the article documents, most security tooling built around size-based heuristics won’t flag it precisely because it’s small. The payload miniaturization trend in kernel exploits — from ~4KB in 2022 to 732 bytes in 2026 — has been deliberately engineered to stay under the thresholds defenders built for the prior generation of exploits. Behavioral detection is the only viable path right now, and only if it’s specifically watching kernel privilege transitions.
Assumption 3: “We’re not exposed because this requires local access, not remote.” In cloud and containerized environments, this distinction has nearly collapsed. The article identifies compromised container images pulled from public registries as a primary delivery vector — and in a Kubernetes cluster, “a container on the cluster runs malicious code” is effectively local access to the shared host kernel. If your infrastructure pulls container images from DockerHub, public ECR, or GitHub Container Registry without content trust verification, you should treat this as a partially remote exploit.
Correcting these three assumptions is the foundation everything else builds on.
Triage by System Role: What to Do First Depends on What You Run
Not every Linux system carries equal risk. The article’s vulnerability table and threat actor scenarios map to different urgency levels based on what role the system plays.
Internet-facing servers and API gateways are the highest priority. They process untrusted input continuously and are the most likely target for the ransomware-operator scenario the article describes — where the exploit represents a monetization window before the patch closes it. Apply all five interim mitigations within 24 hours. There is no defensible reason to wait.
Kubernetes cluster nodes represent the Kernel Escape Multiplier scenario the article warns about: one successful compromise cascades to every workload on the node. Priority actions specific to this role:
- Immediately audit which nodes run kernel versions in the 5.15–6.8 range:
kubectl get nodes -o wide | grep -E "5\.1[5-9]\.|6\.[0-8]\." - Cordon vulnerable nodes if replacement capacity exists:
kubectl cordon <node-name>— this stops new pods from scheduling to them without disrupting running workloads - Restrict pod scheduling to nodes running kernel 6.9+ or a community-patched build using node labels and
nodeSelector/nodeAffinityrules - Enable Kubernetes audit logging to detect the service account token theft the article describes as the lateral movement vector:
--audit-log-pathand--audit-policy-fileon the API server
CI/CD build nodes are the sleeper risk most teams don’t prioritize but should. A compromised build node that gains root via the kernel exploit can tamper with build artifacts, inject backdoors into packages, or exfiltrate secrets from the build environment — all before any output reaches production. Restrict these nodes to pulling from verified, internally-mirrored registries only. Audit every external dependency that build jobs pull at runtime.
Developer workstations running GUI Linux desktops — the one category where disabling clipboard daemons is not an acceptable mitigation, since it breaks core functionality. The compensating path here is applying the sysctl kernel hardening settings below, deploying the community kernel backport (which is the only mitigation that doesn’t break functionality), and ensuring developers are not running production credentials locally.
Headless production servers with no public-facing services carry the lowest urgency if they genuinely have no path for untrusted code execution. Apply sysctl hardening, establish the kernel module baseline, and schedule the official kernel upgrade immediately upon release. Don’t defer indefinitely — the patch vacuum monetization window the RAND research documents means the exploit’s value on dark web markets peaks in the first 14–21 days and doesn’t disappear after that.
Hardening the Initial Access Layer — The Mitigation the Article Doesn’t Cover
Every mitigation in the article focuses on what happens after the payload reaches the kernel. But the payload has to get there first — and hardening the initial access vectors is where defenders can break the kill chain before it reaches the copy_from_user() boundary failure stage.
The article identifies three realistic delivery paths from its threat actor scenarios:
Path 1 — Malicious container image (Ransomware/APT scenario): The exploit is embedded in a container image pulled from a public registry and executes during container startup or normal operation. Defenses:
- Enable Docker Content Trust:
export DOCKER_CONTENT_TRUST=1— only signed images will pull - Scan every image before it reaches any host in the 5.15–6.8 vulnerability range:
trivy image <image>:<tag> --severity CRITICALwith a pipeline gate that fails on critical findings - Maintain an internal mirror of approved base images (Alpine, Ubuntu, Debian variants) and prohibit direct pulls from public registries on production nodes
- Deploy an admission controller (Kyverno or OPA Gatekeeper) that rejects pods referencing unsigned or unscanned images
Path 2 — Malicious CI/CD build step (Insider threat / supply chain scenario): A tampered pipeline step delivers a build artifact that triggers the payload at deployment time. Defenses:
- Require two-person approval for pipeline configuration changes — build definition files are as sensitive as production code
- Pin every build tool, base image, and dependency to a specific digest hash, not a mutable tag
- Run build jobs in ephemeral, single-use environments that are destroyed after each build — persistence is what makes this attack profitable
- Audit service account permissions in your CI/CD platform: build jobs should not have credentials that provide write access to production systems
Path 3 — Spear-phishing to clipboard interaction (Nation-state APT scenario): A malicious document or link triggers a clipboard paste operation that delivers the payload. This is the path most relevant to the clipboard daemon mitigation in the article. Beyond disabling xclip/xdotool on servers, apply these controls on developer systems:
- Restrict browser clipboard API access via browser policy (Chrome’s
ClipboardReadAllowedandClipboardWriteAllowedenterprise policies) - Train developers explicitly that clipboard paste events from untrusted sources carry a new risk category in 2026 that did not exist before this exploit class
- Consider endpoint DLP tools that monitor clipboard content patterns for suspicious code injection sequences
Live Patching: The Mitigation That Eliminates the Reboot Requirement
The article lists kernel live patching (kpatch) as Mitigation #4. For production systems where even a brief maintenance window is operationally difficult, live patching is the highest-value interim mitigation because it applies an in-memory fix without requiring a reboot — no downtime, no service disruption.
Ubuntu systems — Canonical Livepatch (free up to 5 machines, paid via Ubuntu Pro):
sudo snap install canonical-livepatch
# Register at ubuntu.com/security/livepatch to get a token
sudo canonical-livepatch enable <TOKEN>
# Verify status
sudo canonical-livepatch status --verbose
Canonical will push a livepatch for this vulnerability through the same channel as other kernel CVEs — the moment it appears, enrolled systems receive it automatically without a reboot.
RHEL systems — kpatch (included with RHEL subscription):
sudo dnf install kpatch kpatch-patch
sudo systemctl enable --now kpatch
# List available patches
sudo kpatch list
Red Hat’s kpatch infrastructure delivers patches through the RHSA advisory system. Once an RHSA for this CVE is published, the corresponding kpatch module will be available within hours.
Community kpatch for upstream kernels (Ubuntu/Debian systems not on Canonical Livepatch): The community-maintained livepatch module referenced in the article is available via the oss-security thread. Before loading any community module into production:
- Verify the GPG signature on the module against the key published in the oss-security thread
- Test in a staging environment and verify normal system operation for at least 2 hours before production rollout
- Keep the original unpatched kernel available as a fallback boot option — do not remove it from the bootloader until the official upstream patch is confirmed stable
Compensating Controls for the SELinux/AppArmor Gap
Since MAC-layer containment cannot stop this exploit, these controls operate at different layers to either reduce the exploit’s effectiveness or accelerate detection when it fires.
Maximize KASLR effectiveness. The 732-byte payload’s precision engineering — the article’s central finding — depends on knowledge of kernel memory layout. KASLR randomizes that layout on each boot. Verify it’s active and configured for maximum entropy:
grep -i kaslr /proc/cmdline
# Output should include 'kaslr' — if not, add it to GRUB_CMDLINE_LINUX in /etc/default/grub
sudo update-grub # Ubuntu/Debian
sudo grub2-mkconfig -o /boot/grub2/grub.cfg # RHEL/Fedora
Deploy Falco with privilege-escalation rules specific to this exploit’s signature. The article’s detection section notes that eBPF-based monitoring via Falco provides the highest-fidelity early-warning signal available before a CVE signature exists. A Falco rule targeting unexpected root-process creation from non-root parents — the specific pattern a successful ring-0 escalation produces — gives you detection in seconds rather than the five-day dwell time seen in the Mexico breach case study from the broader 2026 threat landscape:
# /etc/falco/falco_rules.local.yaml
- rule: Kernel Exploit Root Escalation Pattern
desc: Detects root-privileged process spawned from non-root parent — consistent with ring-0 escalation
condition: >
spawned_process and
proc.pname != "init" and proc.pname != "systemd" and
proc.pname != "su" and proc.pname != "sudo" and
user.name = "root" and
proc.auid >= 1000
output: >
Potential kernel privilege escalation (parent=%proc.pname pid=%proc.pid
user=%user.name cmd=%proc.cmdline container=%container.name)
priority: CRITICAL
tags: [host, process, privilege_escalation]
Set restrictive ptrace scope. Post-escalation, an attacker with root access can use ptrace to inspect every other running process. Restricting scope limits what the exploit can do after it fires:
sudo sysctl -w kernel.yama.ptrace_scope=2
# Scope 2: only processes with CAP_SYS_PTRACE can trace. Scope 3: no ptrace at all.
echo "kernel.yama.ptrace_scope=2" | sudo tee -a /etc/sysctl.d/99-hardening.conf
Organizational Actions That Need to Run Alongside the Technical Work
Technical mitigations applied without organizational coordination create gaps. These actions need to happen in parallel.
Convene a brief incident-posture call within 24 hours of reading this article. Confirm: who owns kernel patching across all Linux systems? Is there a current inventory of kernel versions in production? What is the change management process for emergency kernel updates (live patches shouldn’t require the same approval cycle as planned maintenance)? These three questions surfaced by a brief call will surface more risk than most organizations expect.
Declare this a P1/Critical vulnerability in your internal tracking system regardless of CISA KEV status. The article correctly notes that the absence of a CISA KEV entry means active exploitation hasn’t been confirmed — not that it isn’t coming. The RAND research on zero-day economics the article cites documents that patch vacuum windows attract the most capable threat actors. Don’t let the absence of a KEV listing translate to downgraded urgency internally.
Update your patch SLA policy for kernel CVEs temporarily. Most organizations operate on 30/60/90-day patch windows tied to CVSS scores. This exploit warrants a custom exception: any kernel vulnerability that bypasses SELinux and AppArmor simultaneously, with no patch available, should carry a de facto 24-hour SLA for mitigations and a maximum 72-hour SLA for live patching wherever available. Document the exception formally so the security team has authority to push through change management without the normal friction.
Prepare your breach notification documentation now, before you need it. If the exploit is weaponized against your environment during the patch vacuum window, regulatory notification timelines (GDPR’s 72 hours, US state breach laws measured similarly) begin at discovery. Having template documentation and a runbook for the notification process reduces response time when the clock is already running.
Monitor the oss-security mailing list directly. Subscribe every person with kernel patching responsibility to oss-security+subscribe@openwall.com. The official patch — and any updates on active exploitation — will appear there before anywhere else, including CISA and distribution advisory channels. The article’s estimated 14–30 day patch window means you may be monitoring for several weeks. Automate an alert if a thread containing “copy_from_user” and “patch” appears on the list.
The One Thing That Changes Everything: Patch Velocity
Every mitigation in this section — and in the article’s five interim mitigations — has a cost. Clipboard daemon disruption breaks GUI functionality. Kernel recompilation requires staging validation. Live patching has module-trust considerations. Seccomp profiles can break application behavior.
The official kernel patch, when it arrives, has none of those costs. It adds proper boundary validation to copy_from_user() before the instruction processes, closes the gap that makes the MAC bypass possible, and arrives through trusted distribution channels. Everything else here is buying time until that moment.
So the single most important mitigation is the one that ensures you apply the official patch within hours of it landing in your distribution’s security channel — not days, not weeks. Set up unattended security updates for kernel packages, subscribe to the advisory feeds listed in the article, and run a practice drill of your kernel update + reboot process now, in staging, so you’re not figuring out a rollback procedure at 2 AM on patch day.
The 732-byte Linux zero-day is dangerous not because it’s undefendable but because it punishes delay. Every layer of defense above buys time. The patch ends the exposure.
Immediate Mitigation Steps for System Owners
If you operate systems that may be affected:
For individuals and small teams:
- Identify which of your systems run the affected software/kernel version.
- Apply the latest available vendor security patches the moment they’re released — subscribe to the official vendor advisory mailing list now.
- Until a patch is released, follow the vendor’s recommended interim mitigations (linked in their security advisory).
- Review logs for any unusual activity matching the indicators of compromise published by the security research team that disclosed this issue.
For enterprise and infrastructure teams:
- Run an asset inventory query to identify exposure across your environment.
- Prioritize internet-facing systems running the affected versions for emergency patching.
- Coordinate with your SOC / detection-engineering team to add IOC-based monitoring for indicators published by the disclosing researchers.
- Document the response in your incident-response playbook for similar future zero-day events.
- If patches will take >7 days to deploy, evaluate compensating controls (network segmentation, WAF rules, EDR detection rules).
This article does not provide proof-of-concept code, exploit payloads, or step-by-step attack instructions. For verified technical detail used in detection engineering, refer to the original vendor advisory and the security researcher’s disclosure paper.
Sources & References
- Exploit-DB / NIST NVD — CVE-2022-0847, CVE-2022-0185, CVE-2023-0179, CVE-2024-1086 — historical CVE technical records and payload analysis
- Linux Kernel Security Mailing List — oss-security@openwall.com — original vulnerability disclosure thread (May 2026)
- NIST National Vulnerability Database (NVD) — nvd.nist.gov — pending CVE record for 2026 copy subsystem boundary failure
- CISA Known Exploited Vulnerabilities Catalog — cisa.gov/known-exploited-vulnerabilities-catalog — active exploitation status monitoring
- RAND Corporation — “Zero Days, Thousands of Nights: The Life and Times of Zero-Day Vulnerabilities and Their Exploits” — Ablon & Bogart — rand.org — zero-day market economics research
- kernel.org — Stable release channel and community patch thread for backported memory boundary hardening (6.9 → 5.15–6.8)
- Cloud Native Computing Foundation (CNCF) Annual Survey — cncf.io — containerized workload adoption and infrastructure statistics

Pingback: MAD Bugs Month of AI Discovered Bugs 2026: 500+ Zero-Days
Pingback: Excel Zero-Day Vulnerability 2026 (CVE-2026-21509): Critical Guide